What's Trending
Since 2009, we have been utilizing our extensive expertise in blockchain technologies to help businesses, both large and small, maximize their efficiency.
Explore More-
Blockchain App Development
-
ERC 4337 Token Development
-
Layer 2 Blockchain Development
-
Blockchain Solutions
-
dApp Development
-
Sui Development
-
Solana Development
-
TON Development
-
Binance Development
-
Ethereum Development
-
Cardano Development
-
EVM Chain Development
-
Hyperliquid Clone Development
-
Hyperledger Development
-
Polygon Development
-
Hedera Development
-
Avalanche Development
-
Algorand Development
-
Stellar Development
-
EOS Development
-
Cosmos Development
-
Smart Contract Development
-
Solidity Development
-
Rust Development
-
Pump Fun Development
-
Crypto Presale Development
-
STO Development
-
ICO Development
-
Cross Chain Bridge Development
-
MEV Bot Development
-
DAO Development
-
DeFi Development
-
DeFi Yield Farming
-
DeFi Lending
-
Cryptocurrency Development
-
ERC 1155 Token Development
-
BEP-20 Token Development
-
ERC 721 Token Development
-
ERC 20 Token Development
-
Stablecoin Development
-
Asset Tokenization
-
Real Estate Tokenization
-
Crypto Token Development
-
Memecoin Development
-
Utility Token Development
-
Coinbase Development
-
DEX Development
-
Crypto Exchange Development
-
Margin Trading
-
P2P Crypto Exchange
-
DeFi Exchange

What's Trending
Since 2009, we have been utilizing our extensive expertise in blockchain technologies to help businesses, both large and small, maximize their efficiency.
Explore More




























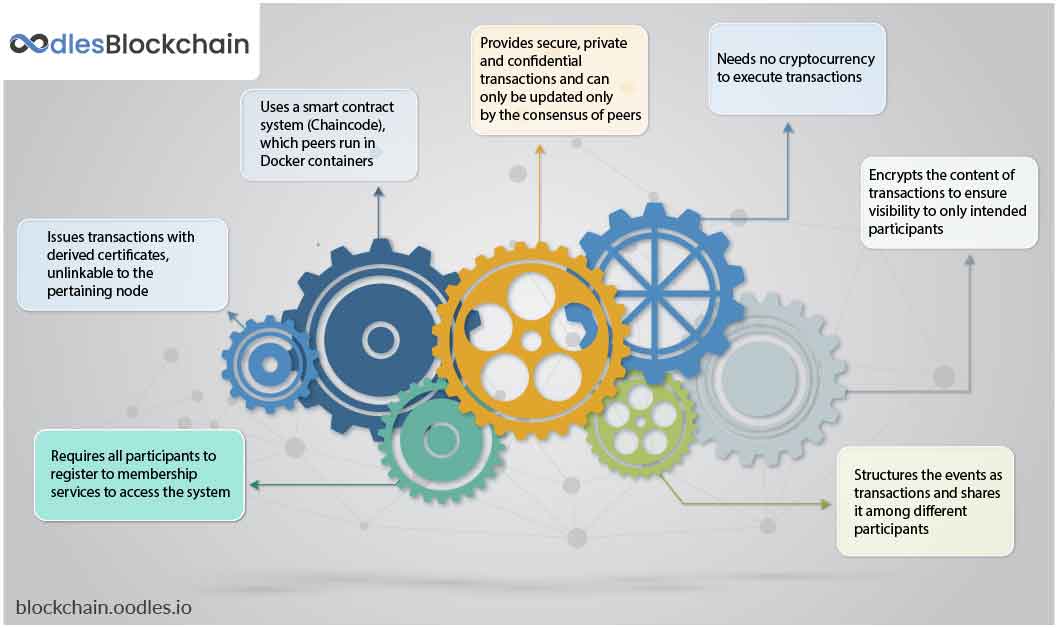 Its design makes it a truly modular, scalable, and secure foundation for enterprise blockchain solutions. It decouples peers into two distinctive runtimes with three separate roles. Commiter peers: Commit transactions, and maintain ledger and state Endorsing peers: Receive, and grant, or deny transaction proposals of endorsements Ordering peers: Approve addition of transactional events to the database, and communicate with other two peer nodes
Its design makes it a truly modular, scalable, and secure foundation for enterprise blockchain solutions. It decouples peers into two distinctive runtimes with three separate roles. Commiter peers: Commit transactions, and maintain ledger and state Endorsing peers: Receive, and grant, or deny transaction proposals of endorsements Ordering peers: Approve addition of transactional events to the database, and communicate with other two peer nodes